Facebook revealed on September 28, 2018 that attackers managed to exploit a vulnerability on the site that allowed them to take over accounts of Facebook users.
The issue, which affected about 50 million Facebook accounts and potentially 50 million more, used a vulnerability in Facebook's "View As" feature that allows Facebook users to view their profile pages as another user.
Facebook users need to select the "three dots" menu on their profile page and select the "View As" option displayed as an option when they do.
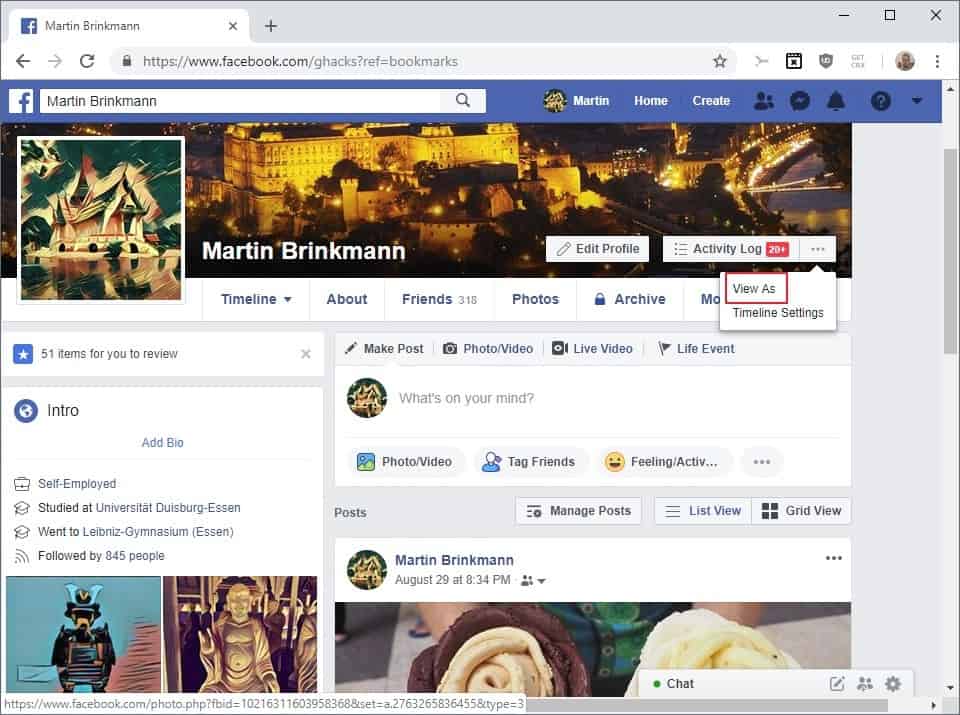
The company turned the feature for now. A notification is displayed to you that the feature has been disabled for the time being.
"Preview My Profile" Disabled
The "Preview My Profile" feature is temporarily disabled. Please try again later.
The attackers managed to obtain access tokens which allow anyone to access an account even without supplying a password.
Facebook's analysis is ongoing at this point in time. The company reacted fast and reset access tokens for affected accounts (nearly 50 million'), and reset access tokens for another 40 million accounts that interacted with View As in the past year.
Investigators have not determined yet whether accounts were misused or if information was accessed. The company plans to update the official security update post on its website once it has more information.
What you may want to do
The attackers managed to gain access to access tokens only. That is why Facebook does not recommend to users to change account passwords as the attackers never got hold of account passwords.
The resetting of the access token blocks access to the Facebook account for anyone who is trying to access it using the old access token.
Facebook displays a login prompt for affected users and a new sign-in to the account generates a new access token that is used from that point on forward.
Facebook users affected by the issue receive a notification about the incident on the next sign-in.
Still, there are some things that you may want to do:
1. Check the last logins
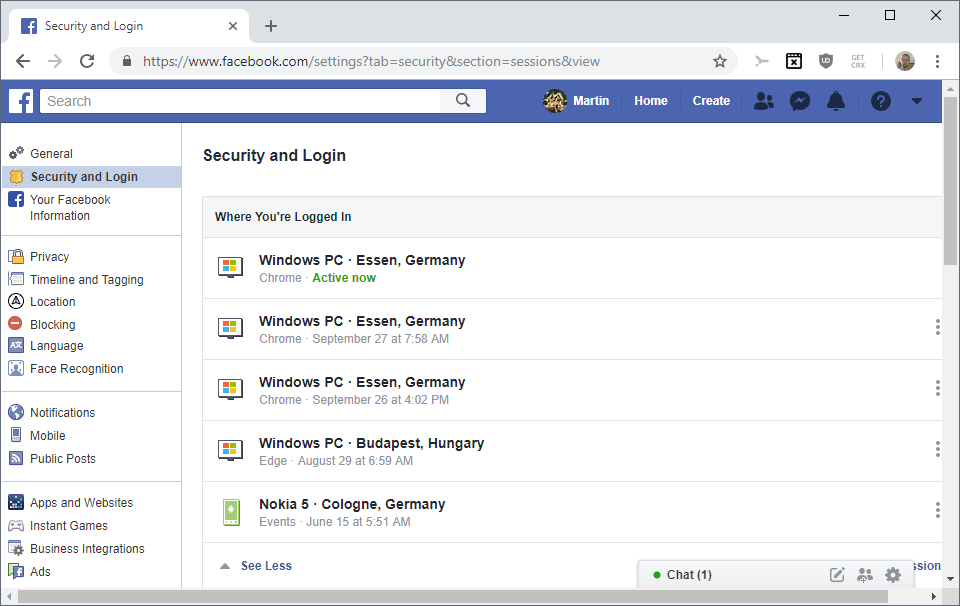
Go to https://www.facebook.com/settings?tab=security§ion=sessions&view and check the devices and locations listed under "where you're logged in".
Make sure that you only see devices and locations there that match your activity. Do the following if you suspect that a logged in session may be by a third-party:
- Click on the three dots on the right of that particular session.
- Select Log Out from the menu.
If you want to start clean, select "log out of all sessions" instead to block any device listed there but the active one from using the access token to access Facebook.
2. Precautions
Facebook supports options to better secure an account.
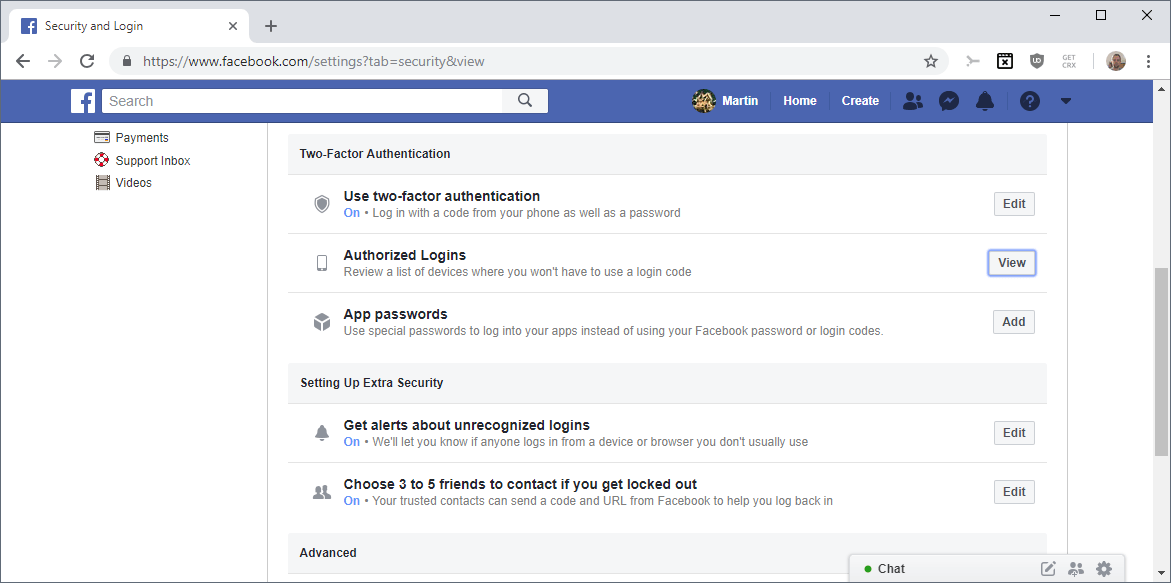
- Get Alerts about unrecognized logins -- Facebook notifies you when it notices logins from devices or browsers that you have not used in the past. Make sure that this is on.
- Authorized Logins -- Check the list of devices where you won't have to use a login code. Remove any device or browser on the list that you don't use anymore or don't have access to.
- Two-factor authentication -- Adds an extra layer of protection to the account. It was discovered recently, however, that Facebook will use the phone number for advertising purposes (advertisers upload lists of phone numbers, and if your phone number is on that list, you will be served ads from that advertiser).
You may also want to be extra careful when it comes to emails or phone calls if you have been affected by the issue. If attackers gained access to the account, they had access to emails, your name, and other personal information that they might use in target phishing or social engineering attacks.
Ghacks needs you. You can find out how to support us here or support the site directly by becoming a Patreon. Thank you for being a Ghacks reader. The post What you should do after the September 2018 Facebook Hack appeared first on gHacks Technology News.
☛ El artículo completo original de Martin Brinkmann lo puedes ver aquí

No hay comentarios.:
Publicar un comentario